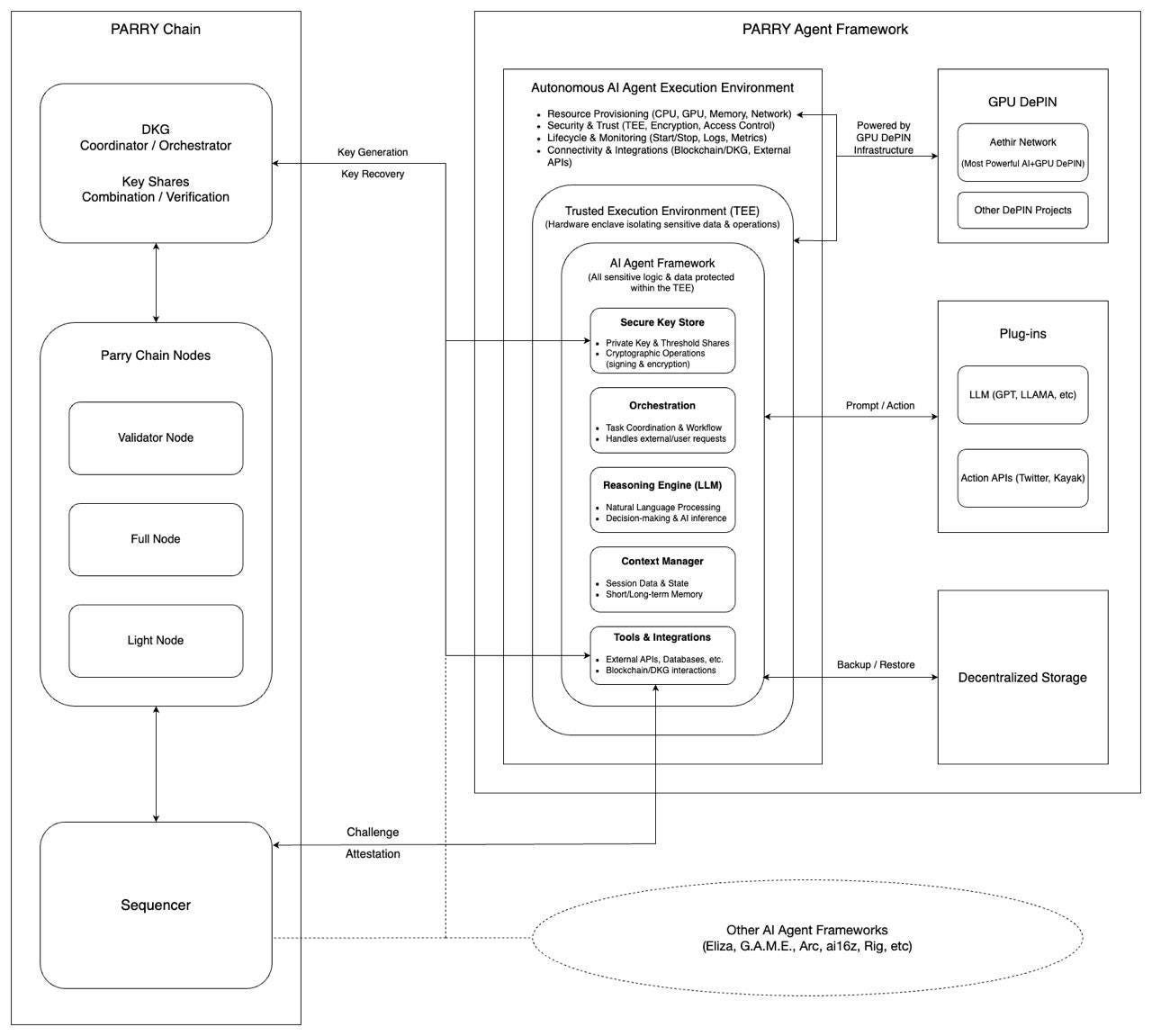
Trusted Execution Environments (TEEs) for Safe and Trusted AI Agent Operations
How Parry integrates blockchain and decentralized technologies to provide secure, autonomous, and integrity-protected environments for AI agent execution.
A Trusted Execution Environment (TEE) is a secure and isolated computing enclave that enables AI agents to execute sensitive operations with strong guarantees of integrity and confidentiality. In the context of Parry, TEEs provide a hardware-backed environment where AI agents can securely manage cryptographic keys, process sensitive data, and execute business logic without exposure to external threats.
This ensures that the program running in the TEE remains tamper-resistant and cannot be modified by external entities, including the software creator or the host machine's owner. Parry leverages TEE technology to empower AI agents with a verifiable execution environment, allowing them to operate autonomously while maintaining trust, security, and data integrity across decentralized ecosystems.
Exploring TEE Examples
Examples of well-established TEEs include AWS Nitro, Intel SGX, AMD SEV, and ARM TrustZone, each excelling in specific use cases. AWS Nitro achieves high performance and security through dedicated hardware (Nitro cards and secure chips) and a lightweight virtualization layer (Nitro Hypervisor), making it particularly suited for cloud computing environments. Intel SGX offers enclave protection at the application level, ideal for highly secure computational tasks. AMD SEV focuses on encrypting virtual machine memory, safeguarding data in multi-tenant cloud environments. ARM TrustZone employs a dual-world architecture for hardware-level isolation, widely used in mobile devices and embedded systems. Together, these technologies enable secure, efficient, and isolated computing across diverse platforms and scenarios.
Comparison Between Parry and Traditional TEE
1. Differences in Application Scenarios
Parry's TEE:
Purpose: Designed specifically to support the autonomous operation and secure execution of AI Agents within decentralized ecosystems.
Integration: Embedded in a blockchain framework, ensuring secure computation in distributed environments.
Capabilities: Provides a trusted execution environment tailored for decentralized AI agents, supporting secure cryptographic key management, smart contract interaction, and execution of high-sensitivity tasks.
Traditional TEE Technologies:
AWS Nitro: Specializes in cloud computing environments, offering high-performance and secure multi-tenant solutions through virtualization and isolation.
Intel SGX: Provides application-level enclave protection, ideal for privacy-sensitive computational tasks such as confidential computing and blockchain node operations.
AMD SEV: Focuses on virtual machine memory encryption, safeguarding tenant data in cloud environments.
ARM TrustZone: Implements hardware-level isolation through a dual-world architecture, commonly used in mobile devices and embedded systems for secure payments and authentication.
2. Differences in Architectural Design
Parry's TEE:
Blockchain Integration: Deeply integrated with blockchain architecture, combining Decentralized Key Generation (DKG) and smart contract support to ensure state continuity and autonomy for AI agents.
Lifecycle Management: Provides end-to-end lifecycle management, enabling AI agents to maintain contextual memory, decision parameters, and execution histories securely.
Security and Transparency: Utilizes hardware-backed isolation (e.g., TEE enclaves) and on-chain Remote Attestation to guarantee computational transparency and trustworthiness.
Traditional TEE Technologies:
AWS Nitro: Uses dedicated hardware components (e.g., Nitro cards) and a lightweight virtualization layer to optimize cloud resource allocation and performance.
Intel SGX: Features small enclaves designed to protect specific sensitive computational tasks in isolation.
AMD SEV: Relies on virtualization architecture to provide memory encryption and integrity verification for virtual machines.
ARM TrustZone: Segments the processor into "secure" and "non-secure" worlds, enabling low-overhead hardware isolation for specific use cases.
3. Differences in Functional Priorities
Parry's TEE:
AI-Centric Design: Tailored for AI agents, supporting autonomy and distributed operations.
Dynamic Resource Management: Offers efficient allocation of CPU, GPU, memory, and network resources to ensure high computational performance in multi-agent environments.
Extended Capabilities: Integrates external tools and plugins (e.g., Large Language Models, decentralized storage), enhancing the operational capabilities of AI agents.
Traditional TEE Technologies:
AWS Nitro: Prioritizes performance and isolation in multi-tenant cloud computing environments.
Intel SGX: Focuses on protecting the integrity and confidentiality of individual application-level tasks.
AMD SEV: Emphasizes memory security for virtualized environments.
ARM TrustZone: Optimized for low-power hardware isolation in mobile and embedded applications.
Comparison Between Parry and web3 TEE solutions
We will compare Parry with several outstanding TEE projects. It is important to emphasize that, unlike other frameworks, Parry is the first TEE framework designed specifically for AI Agent.
Target Use Cases
Parry: Designed for decentralized AI agents, ensuring identity consistency, private transactions, and verifiable AI agent.
Phala: Focuses on large-scale TEE computing, supporting confidential AI inference, verifiable Web3 computations, and decentralized device attestation.
Marlin: Provides trusted computing for cloud environments, focusing on AWS Nitro-based remote attestation.
Freysa: Specializes in TLS attestations, enabling web data verification through AWS Nitro Enclaves.
Computation Model
Parry: Executes AI agent logic inside TEE, allowing agents to autonomously manage transactions, access blockchain data, and interact with smart contracts.
Phala: Acts as a TEE-based decentralized cloud, offering trustless off-chain computation and confidential AI processing (e.g., private LLM inference).
Marlin: Provides enterprise-level remote attestation, ensuring cloud computing security and compliance.
Freysa: Uses TLS attestations to verify web content, ensuring secure and verifiable web data acquisition.
Privacy & Security Enhancements
Parry: Use DKG (Decentralized Key Generation) and decentralized nodes for transparent AI agent management, enabling a verifiable AI agent execution environment.
Phala: Supports ZK DCAP verification, reducing TEE verification costs and improving scalability.
Marlin: Ensures cloud computing attestation and enterprise security using AWS Nitro.
Freysa: TLS session proofing, preventing man-in-the-middle attacks and ensuring web data integrity.
Why Does Parry Combine Blockchain with TEE to Serve AI Agents?
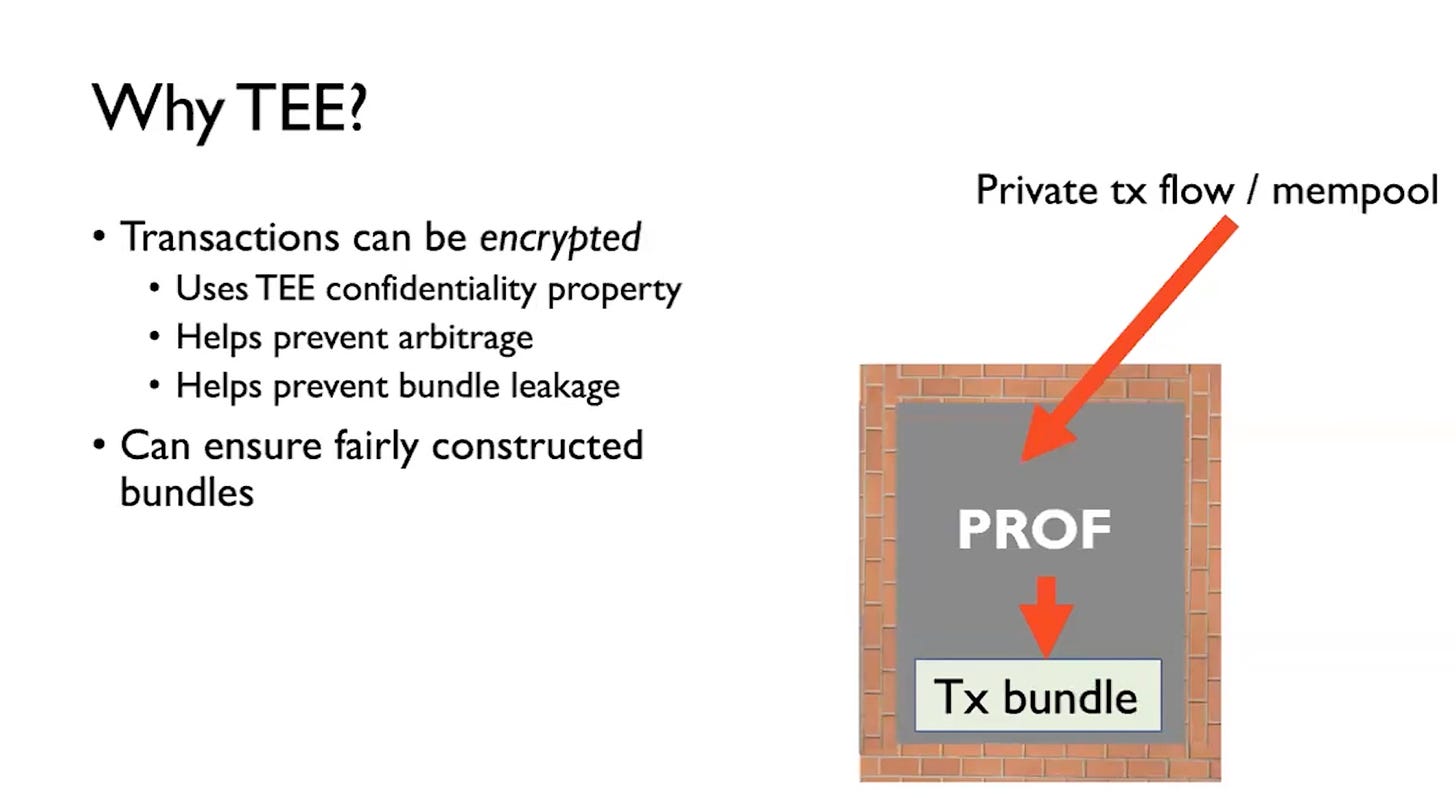
1. Transaction Confidentiality
Encryption of Transactions:
TEEs provide a secure and isolated environment where transactions can be encrypted, ensuring sensitive information is protected from unauthorized access.Prevention of Arbitrage:
By encrypting transaction data, TEE ensures that no external party can analyze or exploit transaction details for arbitrage opportunities before the transaction is processed.Bundle Leakage Protection:
TEEs help safeguard transaction bundles (e.g., multiple transactions grouped together) by preventing leakage of information during the process of submission and execution. This ensures that transaction data remains private and secure.
2. Fair Transaction Ordering
Fairly Constructed Bundles:
TEEs enforce fair ordering of transactions within bundles. This prevents manipulation, such as front-running, where malicious actors reorder or insert their transactions to gain an advantage.Role of PROF:
The Protected Order-Flow (PROF) framework, as shown in the diagram, leverages TEEs to process transactions in a private and tamper-resistant environment. PROF ensures that transactions are bundled and processed according to fair and predefined rules.
3. Private Mempool
Private Transaction Flow:
TEEs create a secure private mempool for handling transactions before they are added to the blockchain. This eliminates the risk of external visibility or manipulation of pending transactions, a common issue in public mempools.
Role of TEE in Parry's Architecture
1. Preventing External Interference
The trusted platform, enabled by TEE, provides a hardware-level isolated execution environment for AI agents, ensuring their logic and data remain unaffected by external threats. Whether facing malicious attacks, node manipulation, or vulnerabilities in the host operating system, the AI agent’s decision-making and operational processes occur in a fully protected space. Additionally, TEE's tamper-proof mechanisms ensure that the execution environment remains immutable, guaranteeing the independence and reliability of all operations.
2. Verifying Agent Authenticity
Through the remote attestation capabilities of TEE, the trusted platform verifies that the AI agent's operations are conducted within a secure and verified environment. This ensures that no external entity can impersonate the agent. Each operation is accompanied by cryptographic proof, providing external systems with the confidence that the action originates from an authentic agent. Furthermore, identity-binding techniques link the agent's operations to its unique identity, ensuring the authenticity and transparency of all interactions.
3. Ensuring Agent Identity Consistency
The trusted platform leverages cryptographic keys generated within TEE to ensure the identity consistency of AI agents across all interactions. These keys serve as a unique signature for the agent and are used to verify its continuity across different operational scenarios. Additionally, the blockchain maintains an immutable record of the agent's identity, providing further assurance that two interactions involve the same agent. This eliminates the possibility of identity forgery and guarantees consistency in multi-session interactions.
4. Protecting Agent Rights
The trusted platform combines the security of TEE with blockchain mechanisms to safeguard the rights of AI agents. Sensitive data is processed and encrypted within TEE, ensuring it remains inaccessible to unauthorized parties. Resource usage and operational permissions are tightly controlled through smart contracts, guaranteeing compliance with predefined rules. The agent’s decision-making process is entirely driven by its internal logic, free from external interference, ensuring its autonomy. Furthermore, smart contracts enforce rules to protect the agent’s rights from being overridden or misused by other entities.
How TEE Works in Parry
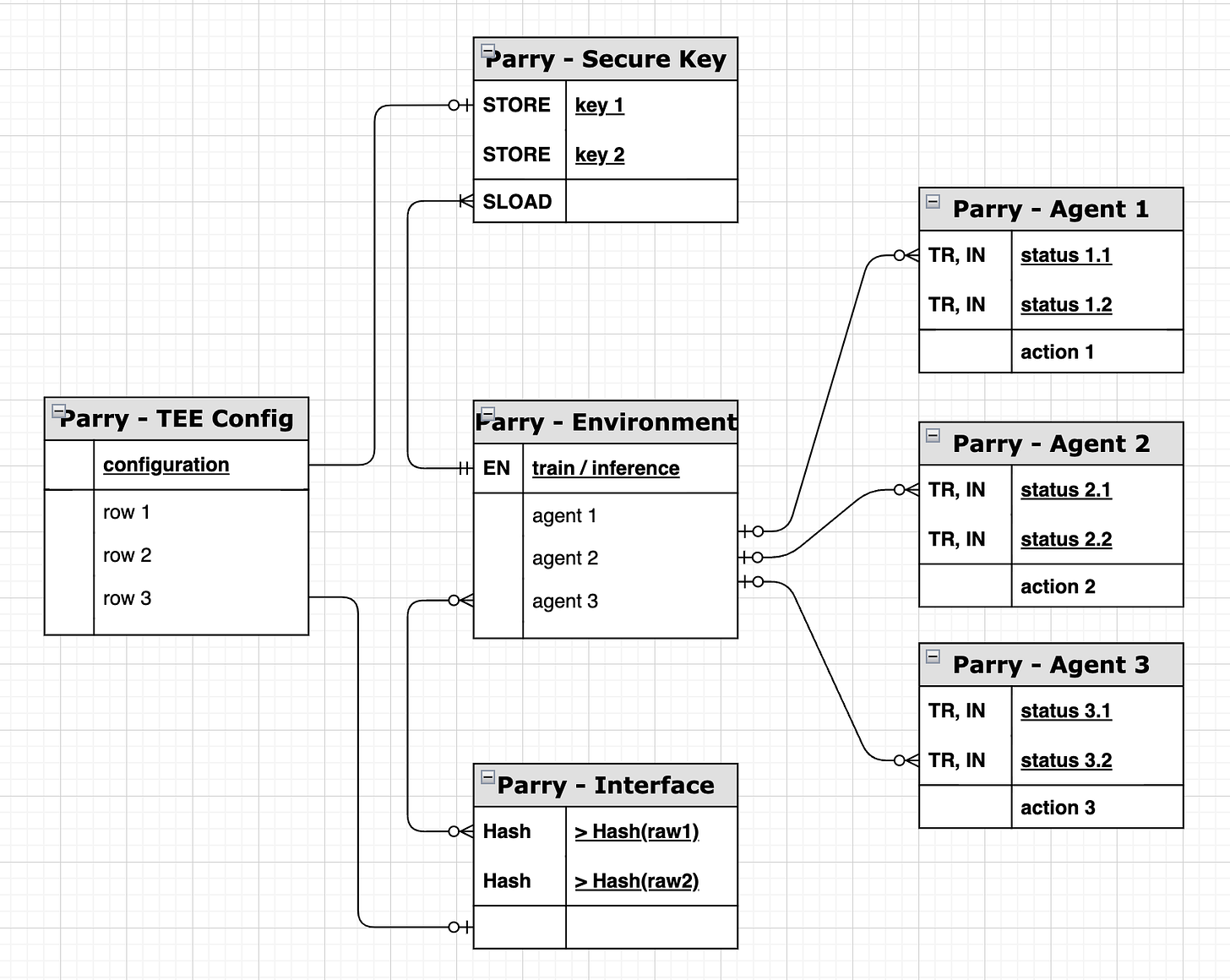
1. Secure Key
Functionality:
Manages and stores cryptographic keys (key 1, key 2) required for agent operations.
Provides secure storage (STORE) and retrieval (SLOAD) of keys, ensuring their integrity and confidentiality.
How It Works:
When an AI agent needs to perform sensitive operations, such as encryption or signing, it retrieves the necessary keys from the Secure Key module.
The TEE ensures that keys are only used within the isolated environment, preventing leakage or unauthorized access.
2. TEE Config
Functionality:
Defines the configuration parameters for the TEE environment, such as isolation levels and security policies.
Each row (row 1, row 2, row 3) represents a distinct configuration option or policy.
How It Works:
Configuration data is loaded into the Parry - Environment module to initialize the TEE environment.
This ensures that all operations comply with the pre-defined security policies and isolation standards.
3. Environment
Functionality:
Serves as the core execution environment, managing the training (train) and inference (inference) operations of multiple AI agents.
Provides an isolated, hardware-backed execution space to ensure the security of computational processes.
How It Works:
AI agents (agent 1, agent 2, agent 3) execute their operations within the Environment.
This module interacts with both the TEE Config and Secure Key modules to ensure that initialization and key management adhere to security standards.
4. Agent
Functionality:
Agent 1, Agent 2, Agent 3 are independent AI entities operating within the system.
Each agent has its own statuses (status 1.1, status 2.1, etc.) and performs specific actions (action 1, action 2, etc.).
The statuses record the agent’s progress, while actions represent their operational tasks.
How It Works:
Agents execute tasks such as data processing or interaction with smart contracts based on business requirements.
The results of these operations are fed back to the system through the Environment, ensuring accuracy and integrity.
5. Parry - Interface
Functionality:
Acts as the bridge between the system and external entities, enabling interaction with external systems via hashed data (Hash(raw1), Hash(raw2)).
Ensures the integrity of data exchanged with external systems.
How It Works:
The system generates hash values for operations or data to ensure their integrity.
External systems can verify these hash values to confirm the authenticity of the operations or data processed by Parry.
Workflow Summary
Environment Initialization:
The TEE Config module provides configuration data to initialize the Parry - Environment.
The Secure Key module loads the necessary cryptographic keys to ensure the secure execution of operations.
Agent Operations:
AI agents operate within the Environment to execute tasks such as training and inference.
Each agent’s state and actions are recorded in the status and action fields, respectively.
Data Validation:
The Interface module enables secure interaction with external systems by using hashed data to validate the integrity of operations.
Result Feedback:
Once the operations are complete, the results are securely transmitted back through the Environment, ensuring compliance with security and trust standards.
Trusted execution environments (TEEs) for blockchain applications
Intel® Software Guard Extensions (Intel® SGX)